The Network Inventory program has the license key auditing function. To use it, you need to bring up the License Manager window. Click the License Manager button on the Main tab of the toolbar. Select a program and click the "Monitor Reg. Keys" button. Enter valid registration keys for the program. After that, you will be able to see how the entered license keys are used on computers.
Let's take a closer look at the process of configuring the program for license key auditing. To configure the license key monitoring you need to perform the following steps:
1) Configure gathering the license information from remote computers. If you have already done this please follow to the Step (3). Otherwise, close the License Manager and go to the program settings by selecting the "Service - Settings" menu item. Select the "License Information" section and configure how the program should gather the license information for necessary programs. Close the program settings after that.
2) Open the License Manager again and configure software you want to audit. Enter numbers of licenses you own for each program. Also, you need to configure how the program should get serial keys for the programs you want to audit. Learn more about configuring the License Manager for license auditing...
3) Select a program in the list of audited software on the License Manager window and click the "Monitor Reg. Keys" button. The program will show available serial numbers used on computers. By default, they will be highlighted with red color. The red color means that the keys (serial numbers) are not contained in the list of valid keys.
Click "Edit" and add valid keys to the text area on the window displayed. You can prepare a list of valid keys in a text file and then copy its content to the window using the clipboard.
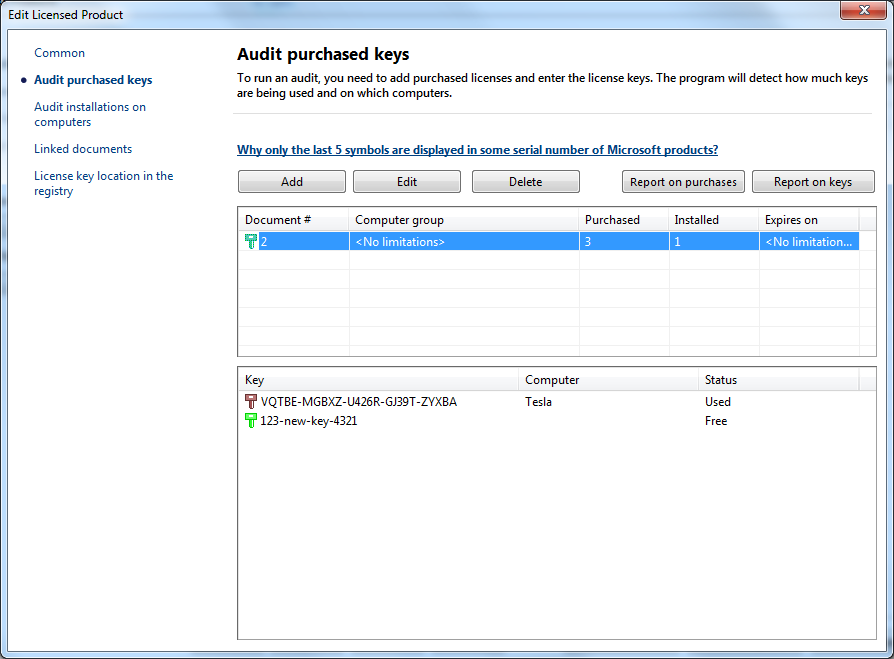
After adding the valid key list, the program will analyze the database and show the numbers of times each key is used on computers. For your comfort, unused keys are highlighted with green color. Keys that used on several computers are displayed yellow. Keys used only on one computer are displayed black. Keys not contained in the valid key list are displayed red. Select a key in the list and see the list of computers where this key is used.