Network Bandwidth Monitoring
![]() The program's main function is the monitoring and displaying of inbound and outbound network traffic which transmits through hosts. Its operation is based on periodical polling of traffic sensors on each host in the network. The traffic Sensor is a function which gathers the current traffic volume on a host's network interface. You can configure several different sensors for each host. Each sensor takes into account the inbound and outbound traffic from only one network interface.
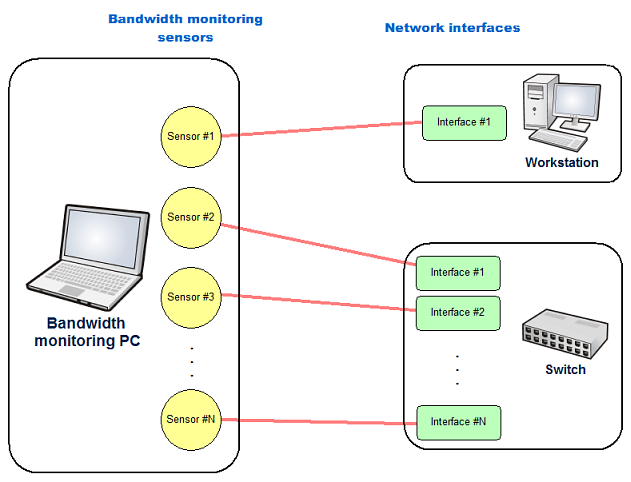
The program's main function is the monitoring and displaying of inbound and outbound network traffic which transmits through hosts. Its operation is based on periodical polling of traffic sensors on each host in the network. The traffic Sensor is a function which gathers the current traffic volume on a host's network interface. You can configure several different sensors for each host. Each sensor takes into account the inbound and outbound traffic from only one network interface.
The following types of network monitoring sensors are currently supported by the program:
- 1. SNMP Sensor
This sensor connects to an SNMP agent of a remote or local computer or another managed network device (switch, router, etc.) and gathers the values of inbound and outbound traffic via the SNMP protocol. There are a lot of network devices that support the SNMP protocol. These may include: servers and workstations working under any operating system, managed switches, routers, printers, web cameras, access points, etc. The SNMP protocol's advantage is its platform independence. To use the SNMP sensor, the SNMP agent must be available on a remote device. Also, you need to know its Community string. The SNMP protocol usually operates via the UDP port 161. That is why this port must be opened in your firewall.
SNMP support in Windows
The SNMP service is an SNMP agent available on Windows workstations. It provides the access to the traffic information and is not installed by default. To install the SNMP service on a Windows computer, you need to follow the instructions described in the Installing and Configuring SNMP in Windows topic. The security SNMP settings are described in the same topic.
To configure the SNMP sensor parameters, you need to provide the host IP address or name, and its Community string. Usually, if the community has not been changed, the standard string is "public".
The Timeout and Attempts parameters are used for fine-tuning the sensor settings in networks with large traffic or with weak physical channels. You can configure the number of polling attempts and the interval between the attempts. If the first polling fails, the program will run that polling again after the configured interval of time (Timeout). This helps to avoid receiving false alerts when a temporary network outage occurs. If all the attempts finally fail, the sensor polling will be considered as failed.
Advantages of gathering the traffic data via SNMP:
- You can poll a great number of different devices supporting SNMP: switches, network printers, computers and servers operating under Windows, Linux, etc.
- Often, you will not even need to configure remote computers. Otherwise, you will only need to enable the SNMP agent or run the corresponding service (Windows) or daemon (Linux).
- You do not need to install any additional software on remote computers except the cases when the "SNMP service" is not installed by default on a Windows system (see the above links to learn about the installing SNMP).
- SNMP does not consume much system resources.
- You do not need administrator rights on the local and remote computers.
- The SNMP polling process is hidden for network users.
Disadvantages:
- Sometimes SNMP agents are disabled by default in devices.
- The SNMP protocol's versions 1,2, and 2c are not secure. The information is not encoded in them. The protected version of the SNMP protocol is SNMPv3.
- 2. WMI Sensor
Windows Management Instrumentation (WMI) is a set of interfaces for the operating system management through the special components (via a network or locally). With the help of this mechanism, the sensor obtains the traffic values on a particular network interface. However, WMI runs under the Windows operating system only. Therefore, this sensor can keep track traffic only of remote computers with Windows OS installed. For WMI sensors, you may need to configure WMI and other particular services on the local and remote computers for a successful operation. You can find out more about this issue in the WMI settings for working with a remote computer topic.
To configure the WMI sensor, you need to specify the IP address or the host name. Also, a username and the according password are required for authorization on the remote computer.
Warning! Please keep in mind the following features of the WMI mechanism. The WMI connection runs under the account with the provided credentials, but the operation itself runs under the name of that user, under whom the program is running on the local computer. This final user should have administrator rights on the remote computer. The Bandwidth Monitor service has to be started under this user account. Learn more about this issue here: Program settings.
Advantages of gathering the traffic data via WMI:
- Often, you will not even need to configure remote computers (especially when computers belong to a domain). However, you should have administration rights on remote computers to poll the traffic data via WMI.
- You do not need to install any additional software on remote computers.
- Users without administrator rights cannot affect the process of gathering the traffic information.
- The WMI polling process is hidden for network users.
Disadvantages:
- Administration rights on remote computers are required.
- The security policy will probably require some configuration (the "classic" access model instead of the "guest" model). The Firewall will probably need to be configured as well (allow DCOM connections). Learn more: WMI troubleshooting.
- WMI operates in a Windows environment only.
- 3. Remote Agent
If you cannot use the SNMP protocol or WMI in your network, the traffic values can be collected with the help of the remote agent service. The remote agent is a service that gathers traffic data locally and then sends it via the TCP protocol using the 54231 port to the main application upon request (client-server). The TCP port can be changed. You need to install the remote agents on remote computers to gather the traffic data from them.
Advantages of gathering the traffic data via remote agents:
- No administration rights on remote computers are required.
- The agent is implemented as a Windows service and does not require the monitored computer to be logged on.
- The traffic polling process is hidden for network users.
Disadvantages:
- You need to install the agent service on all monitored computers.
- You need to enable the agent's TCP port (54231 by default) in the Firewall on the local and remote computers.
- The agent service operates in a Windows environment only.
- When many inactive remote agents are polled simultaneously, the polling errors can arise sometimes in some versions of Windows. This is caused by the limitations on the number of allowed outgoing half-open TCP connections. Learn more about the limitations and Windows versions affected in the System limitations on accessing remote TCP/IP opened ports topic.
The remote agent service installation procedure is described here: Installing and Configuring Agents. Installing WinPCap Driver.
- 4. Packet Sniffing
This type of sensor allows you to monitor traffic for different network protocols independently. For example, you will be able to draw network bandwidth charts for the HTTP, FTP, POP3 protocols. This type of sensor also allows you to distinct local traffic from the Internet traffic. The sensor operation is based on the packet sniffing and counting all packets sent and received by a certain network interface on a computer with a remote agent installed along with the WinPcap sniffing driver. This sensor does not count other computers' traffic. WinPcap is a 3rd party free opensource library (www.winpcap.com).
To get the Packet Sniffing sensor working on a remote Windows PC, you need to install our agent and the WinPcap library on that PC. The agent operates as a service in the background mode. It collects traffic values for network interfaces and periodically sends them to the main program upon its request using the TCP protocol. The service receives requests on the TCP port 54321. The port number can be changed in the program setings.
Advantages of gathering the traffic data via the packet sniffing sensors:
- Monitor traffic for different network protocols independently.
- Distinct counting local network traffic from the Internet traffic.
- Ignore traffic from the list specified hosts.
- Advantages of the remote agent service are included:
1) No administration rights on remote computers are required.
2) The agent is implemented as a Windows service and does not require the monitored computer to be logged on.
3) The agent continues to collect and save statistics even if the main bandwidth monitoring service is not running. At the first connection to the agent, it transfers all autonomously collected statistics to the program.
4) The traffic polling process is hidden for network users.Disadvantages:
- You need to install the WinPcap driver on all monitored computers.
- Disadvantages of the remote agent service included:
1) You need to install the agent service on all monitored computers.
2) You need to enable the agent's TCP port (54231 by default) in the Firewall on the local and remote computers.
3) The agent service operates in a Windows environment only.
4) When many inactive remote agents are polled simultaneously, the polling errors can arise sometimes in some versions of Windows. This is caused by the limitations on the number of allowed outgoing half-open TCP connections. Learn more about the limitations and Windows versions affected in the System limitations on accessing remote TCP/IP opened ports topic.The remote agent service and WinPcap installation procedure is described here: Installing and Configuring Agents. Installing WinPCap Driver.
![]() Traffic sensors are polled by several threads simultaneously. The number of polling threads can be configured in the program settings.
Traffic sensors are polled by several threads simultaneously. The number of polling threads can be configured in the program settings.
You can configure the polling interval for each sensor individually. This helps decrease the sensor polling traffic during the program's operation and decreases the CPU load.